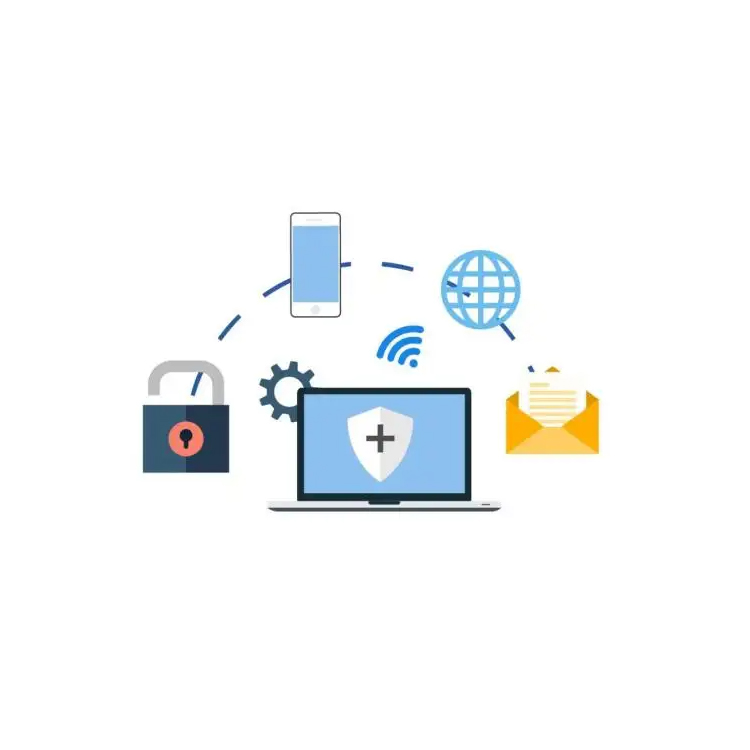
Currently, many organizations have migrated their business systems to cloud platforms, making the cloud an essential IT infrastructure for them. Cloud computing technology has brought revolutionary changes to traditional IT infrastructure, applications, data, and operational management, presenting both challenges and opportunities for security management. Firstly, cloud computing introduces new threats and risks, which also impact and disrupt traditional information security systems, implementation methods, and operational management systems. Secondly, the elasticity of cloud resources, on-demand allocation, high reliability, and resource centralization all indirectly enhance or benefit security protection. However, they also pose challenges and issues for the improvement and upgrading of security measures, the design and implementation of security applications, and security operations and management.
According to survey data, cloud computing security risks are a major concern for customers. Ensuring cloud computing security has become one of the critical issues that organizations urgently need to address in the planning, design, construction, and use of cloud computing systems.

Solution
The cloud computing security protection scheme design adheres to a business-centric, risk-oriented, and depth-active defense concept based on security domains. It takes into account the security threats, demand characteristics, and related requirements of cloud platforms, optimizing the design of the security protection system architecture, content, implementation mechanisms, and related product components.
The寸草心Cloud Defense Security Solution features a three-tiered defense system from the outside in, primarily consisting of traditional physical boundary security devices, security resource pools, distributed firewalls, and the vSecCenter Cloud Security Management Platform.
Physical Security Equipment: The one-to-many virtual physical security equipment addresses cloud environment boundary security issues.
Secure Resource Pool: Supports various security resources including physical security devices, virtualized security devices, and SaaS security services, accepting management from various security sub-platforms and providing corresponding security capabilities externally.
Virtualized Distributed Firewall: Solves east-west security protection within cloud environments. The vDFW achieves automated deployment and distributed centralized management, utilizing the traffic redirection module of the inchHeart Firewall to secure east-west traffic.
vSecCenter Cloud Security Management Platform: Manages security resources, offering functions closely related to specific security applications, such as security policy management, configuration management, access control management, and security log management. It can be flexibly configured and expanded based on different application scenarios.